
OWASP Top 10 Security Risks Explained (Real Examples + Fixes)
Learn the OWASP Top 10 security risks with real-world attack examples like SQL Injection, XSS, and CSRF. Discover how to protect your web application from data breaches.
Explore our latest insights, tutorials, and industry best practices.

Learn the OWASP Top 10 security risks with real-world attack examples like SQL Injection, XSS, and CSRF. Discover how to protect your web application from data breaches.


A Practical Architecture Guide to Choosing Between Server-Side Rendering, Static Site Generation, and Incremental Static Regeneration in Modern Next.js Applications


How Blue-Green deployment enables zero downtime releases using Docker, CI/CD pipelines, and traffic switching. A practical guide with real-world examples and rollback strategies.


A technical inference of Lovable's likely layered architecture: Intent Parsing, Context & State Engine, Constraint & Design System, Prompt Orchestration, Model Routing, and Deterministic Rendering.


When database queries slow down, use Views, Materialized Views, and Summary Tables. Learn when to use each, how to make them fast, and how to avoid common mistakes.
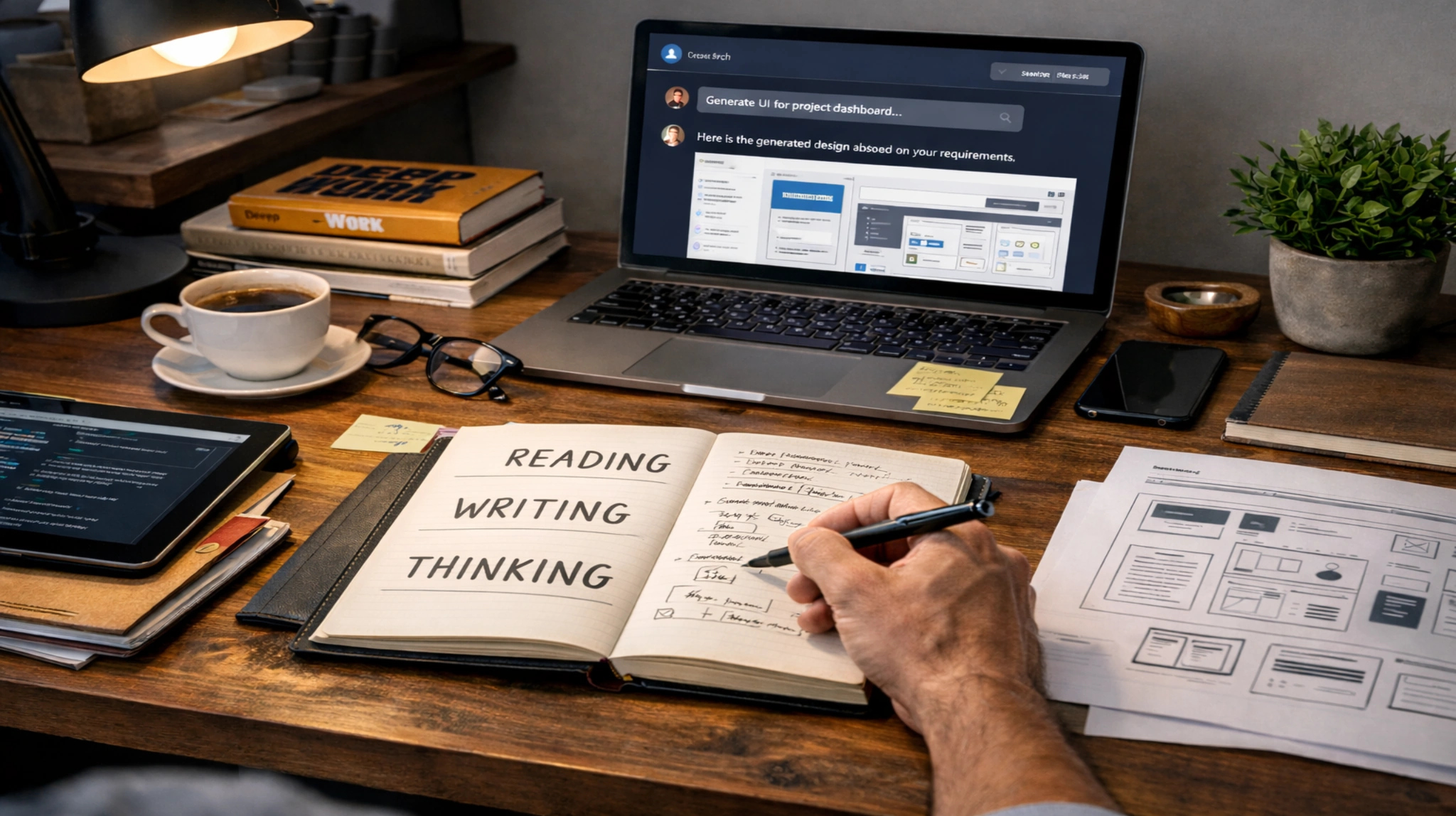

Why the AI bubble is killing your thinking process, and how the fundamentals, reading, writing, and thinking, remain the only way to get the best out of AI.